
VIRTUAL PRIVATE NETWORK (VPN)
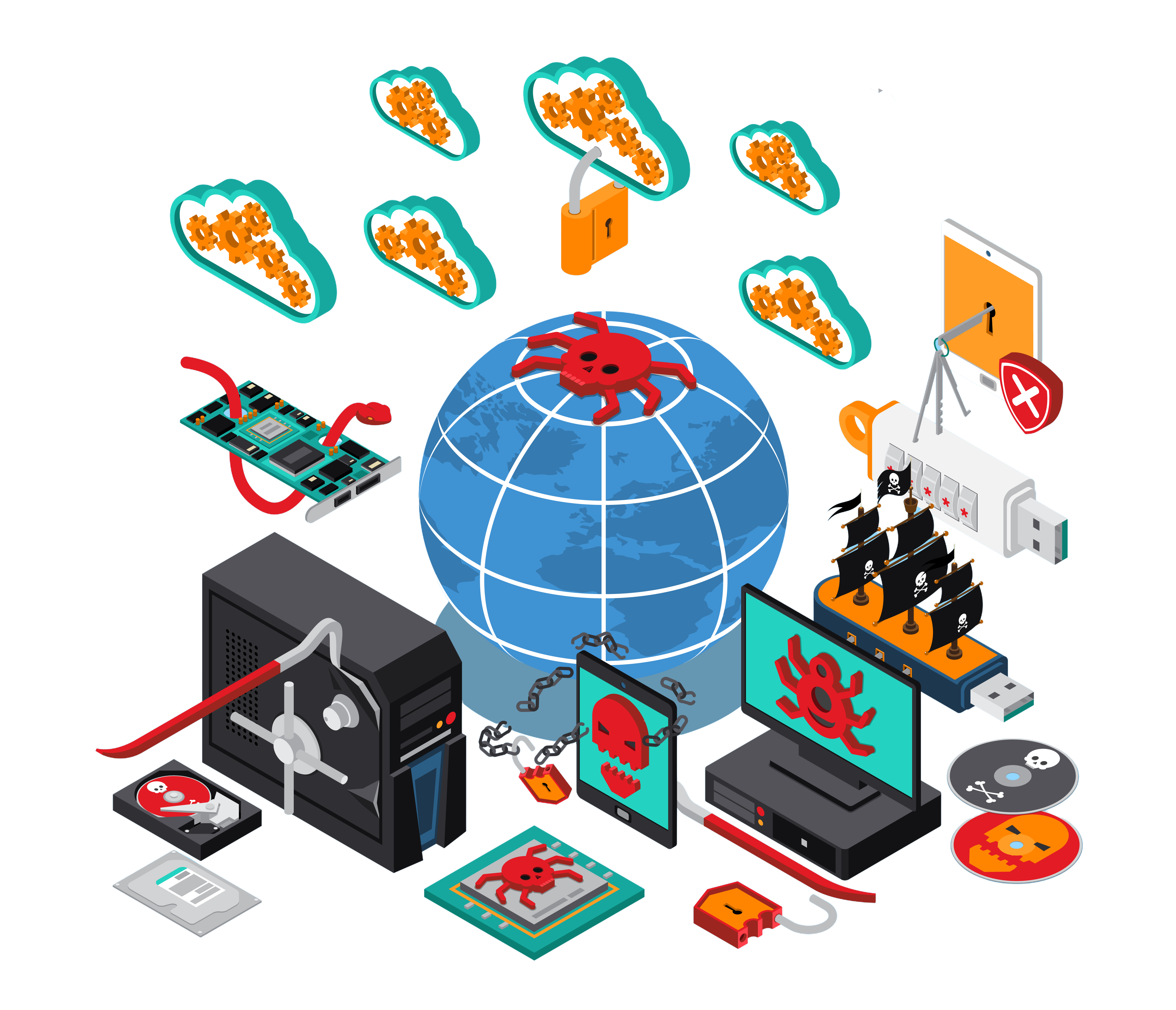
A virtual private network (VPN) lets you experience the internet with privacy, security, and freedom. It also blocks malicious websites, stop web trackers, and monitor your data leaks
- Encryption
- Privacy and Anonymity
- Security on Public Networks
- Avoiding Bandwidth Throttling
VPN is a Secure Connection for your Employees to Work from Anywhere
Virtual Private Network
What is a VPN?
- A VPN is a tool that allows users to create a secure, encrypted connection to another network over the internet. It masks your IP address and encrypts your internet traffic, making your online activities more private and secure.
How VPNs Work
- VPNs route your device’s internet connection through a private server instead of your Internet Service Provider (ISP)
- Data sent over this connection is encrypted, meaning that even if it is intercepted, it can not be easily read
- Your real IP address is hidden, and the VPN server’s IP address is used instead, enhancing anonymity
Types of VPNs
- Remote Access VPN: Allows users to connect to a private network from a remote location, often used by employees to access corporate resources
- Site-to-Site VPN: Connects entire networks (such as two office locations) securely over the internet
- Personal VPN: Used by individuals to browse securely, maintain privacy, and bypass geo-restrictions

Encryption
- VPNs typically use strong encryption protocols, such as:
- OpenVPN: One of the most popular and secure VPN protocols
- IKEv2/IPSec: Known for speed and security
- WireGuard: A newer, efficient protocol designed for simplicity and performance

2 Factor Authentication (2FA)
Two-factor authentication (2FA) is a security method that requires two forms of identification to access data and resources. It's a type of multi-factor authentication (MFA) that helps strengthen account security by requiring users to provide more than just a password.
- Encryption
- Privacy and Anonymity
- Security on Public Networks
- Avoiding Bandwidth Throttling
Benefits of 2FA
- Businesses use 2FA to help protect their employees' personal and business assets. This is important because it prevents cybercriminals from stealing, destroying, or accessing your internal data records for their own use.
- Max passcode entry prevents cybercriminals from hacking and accessing sensitive data. The process is manageable and user-friendly.


Authentication methods for 2FA
There are different authentication methods when using two-factor authentication. Here is a list of some of the most popular options.
- Hardware tokens: Businesses can give their employees hardware tokens in the form of a key fob that produces codes every few seconds to a minute. This is one of the oldest forms of two-factor authentication.
- Push notifications: Push two-factor authentication methods require no password. This type of 2FA sends a signal to your phone to either approve/deny or accept/decline access to a website or app to verify your identity.
- SMS verification: SMS, or text messaging, can be used as a form of two-factor authentication when a message is sent to a trusted phone number. The user is prompted to either interact with the text or use a one-time code to verify their identity on a site or app.
- Voice-based authentication: Voice authentication works in a similar way to push notifications, except that your identity is confirmed through automation. The voice will ask you to press a key or state your name to identify yourself.
SSL Certificate
Secure Sockets Layer (SSL) is a standard security technology for establishing an encrypted link between a server and a client—typically a web server (website) and a browser, or a mail server and a mail client (e.g., Outlook).
- Data Encryption
- Secured Https Protocol
- Compliance & Regulations
- Enhanced user confidence


SSL certificates
SSL certificates are vital for securing online interactions, ensuring data privacy, and building trust with users. They provide data encryption, protect against cyber attacks, and help maintain regulatory compliance. Additionally, SSL certificates contribute to better SEO rankings, increased customer confidence, and overall protection of your website’s reputation. SSL (Secure Sockets Layer) certificates are essential for securing data transmission on websites and providing trust to users.
Why are SSL Certificates Important?
Data Encryption
- SSL certificates encrypt data transmitted between the user’s browser and the web server, making it unreadable to anyone who intercepts it.
- Encryption protects data integrity, preventing hackers from tampering with or corrupting data during transmission.
Authentication and Trust
- SSL certificates authenticate the website’s identity. This ensures that users are communicating with the legitimate website and not with an imposter (a phishing or man-in-the-middle attack).
- The certificate is issued by trusted Certificate Authorities (CAs) after verifying the legitimacy of the website owner, providing users with confidence that the site is safe to interact with.

Secure HTTPS Protocol
- Websites with SSL certificates switch from HTTP to HTTPS, where the stands for secure. Browsers display a padlock symbol in the address bar, indicating a secure connection. This reassures users that the website is trustworthy and their data is protected.
- Without HTTPS, browsers often display warnings about unsecured connections, which can deter users from interacting with the site.
Protection Against Data Breaches
- SSL prevents hackers from intercepting sensitive data during transmission. This is especially important for online businesses, e-commerce platforms, and websites handling financial transactions, as it helps to prevent data breaches and financial losses.
Compliance with Regulations
- Many industries, particularly finance, healthcare, and e-commerce, have data protection regulations (like GDPR, PCI DSS, HIPAA) that require the use of SSL certificates to secure sensitive data.
- Using SSL ensures compliance with these regulations, reducing the risk of legal consequences, fines, and reputational damage.
SEO and Search Ranking Benefits
- SSL prevents hackers from intercepting sensitive data during transmission. This is especially important for online businesses, e-commerce platforms, and websites handling financial transactions, as it helps to prevent data breaches and financial losses.
- In contrast, websites that do not use SSL may be penalized in search rankings, lowering their chances of being found by potential customers.


Enhanced User Confidence
- SSL certificates instill trust in users, especially for e-commerce websites or platforms that handle sensitive data. The presence of a secure connection (HTTPS and the padlock symbol) encourages users to proceed with transactions, knowing their information is protected.
- When a website lacks SSL, browsers may issue warnings, which can cause users to abandon the site, reducing trust and conversions
Protection Against Phishing Attacks
- SSL certificates provide a layer of protection against phishing attacks. Since SSL certificates require verification of the website's identity, it becomes harder for malicious actors to impersonate legitimate websites.
- Users can easily identify the authenticity of the site by looking for the HTTPS and padlock icon, reducing the likelihood of falling victim to phishing scams.
Improved Conversion Rates
- Studies show that users are more likely to complete purchases or share personal information on websites that display signs of security, such as SSL certificates. This can lead to higher conversion rates, particularly for e-commerce and subscription-based services.
Encryption for All Types of Data
- SSL certificates don’t just protect sensitive data like passwords and credit card numbers; they encrypt all types of data shared between users and websites, including browsing habits, emails, and other personal information. This comprehensive protection helps maintain privacy and security online.


Prevention of Man-in-the-Middle Attacks
- SSL protects against Man-in-the-Middle (MITM) attacks, where a malicious actor intercepts communication between a user and a server to steal or alter information. With SSL encryption, even if data is intercepted, it remains encrypted and unreadable to the attacker.
Different Levels of SSL Validation
- SSL certificates come in different types and validation levels, such as Domain Validation (DV), Organization Validation (OV), and Extended Validation (EV). The higher the validation level, the more rigorous the verification process, and the greater the level of trust it offers to users.
- EV SSL certificates, for example, show the company’s name in the address bar, providing additional trust for users, especially on banking or e-commerce sites.